As many of you know, I successfully accomplished one of my life-long goals in passing the (ISC)² Certified Information Systems Security Professional (CISSP) exam in August. One of the common things I have been asked by others aspiring to conqueror this exam is what study methods were successful for me.
In retrospect, I can say there was no one method that was more successful than the other as they all served a specific purpose but what I will say is considering that I live a pretty busy life, I leaned a lot on my Amazon Echo to go through e-books on the subject.
Many of you are probably thinking to yourself that I’m crazy but I assure you on this topic, I am not. The Amazon Echo (Alexa) is one of the most underrated and most powerful tools available on the market. Not only can it tell you the weather, lock your front door, play music and tell you when a local store is open but it can read books you purchase through online bookstores and that is where the magic begins.
Having a busy life with a full time job and keeping up with my children’s daily activities, I was limited in the amount of time I could use to study. When I first started, I would find myself getting too tired reading through books on the topics; cumulatively, the time lost due to pure daily exhaustion was an excess of 10 hours per week. Forward thinking, I knew that I had to find another way, so I explored the option of using my Alexa to read the topic material on my behalf as I followed along.
I’ll start by saying that I highly recommend getting Kindle Unlimited. With an Amazon Kindle Unlimited subscription, users have access to a wide variety of e-books on virtually any topic you can think of. A quick search on CISSP yields a great selection of books that can be downloaded on demand. Python, Security +, Java-Script and yes the CISSP; all there and available for download. Once you discover the right book for you, download the Amazon Alexa app from your tablet or phone’s App Store and start the process of having it read for you.
Use Amazon Alexa App as a Reader
- From the Apple/Android App Store, download Amazon Alexa by Amazon.com
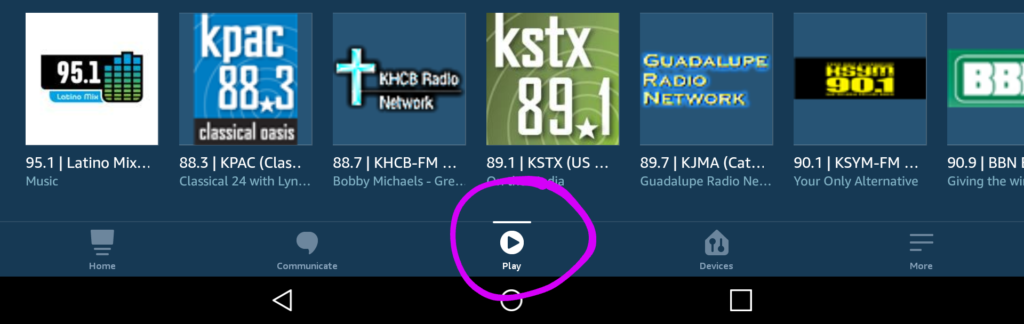
- Open The Amazon Alexa App and select the Play Icon.
- Scroll Down until you see the Kindle Library
- Select your desired book on the carousel by rotating the selection
- A Play On prompt will come up asking you which device you want to listen from. Scroll down until you see the option, This Device.
Once Alexa starts reading the book, load up the Kindle App and follow along. When you launch the App, a prompt should automatically come up recommending you to jump where Alexa currently is reading from. Affirm the option and enjoy learning.
Multitasking With The Amazon Echo
Another cool feature if you have Echo products at home, is that you can have Alexa play it on other devices, maximizing your opportunities to learn. For instance, if you have to start dinner and have an Echo Dot near the kitchen, send a command to your Alexa product to continue reading where you left off. It’s as simple as that.
Just like the popular security adage says about layers in defense, I am a big proponent of learning the same way. Utilize multiple books on the topic of your choosing to maximize perspective and your learning. Follow along with Alexa using a phone, computer or tablet and elevate your knowledge. You will quickly find that this method saves you time and money in your studies. Good Luck!
To support this blog, this post may contain affiliate links. Please read our Privacy Policy for more information.






